Unpatched Unauthorized File Read Vulnerability Affects Microsoft Windows Operating System
Unofficial fixes have been released to fix an incorrectly fixed Windows security vulnerability that could allow Information Disclosure and Elevation of Local Privilege (LPE) on vulnerable systems.
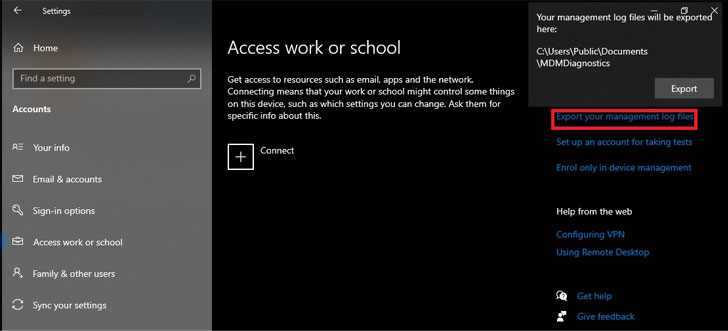
Plotted as CVE-2021-24084 (CVSS score: 5.5), the flaw concerns an information disclosure vulnerability in the Windows Mobile Device Management component that could allow an attacker to gain unauthorized file system access and read arbitrary files.
Security researcher Abdelhamid Naceri was credited with discovering and reporting the bug in October 2020, prompting Microsoft to address the issue as part of its February 2021 Patch Tuesday updates.

But as Naceri observed in June 2021, not only could the patch be bypassed to achieve the same goal, the researcher this month discovered that the incompletely patched vulnerability could also be exploited to gain administrator privileges and run malicious code on Windows 10 machines running the latest security updates.
“Namely, as we have learned from HiveNightmare / SeriousSAM, arbitrary file disclosure can be upgraded to local privilege escalation if you know what files to take and what to do with them,†said Mitja Kolsek, co-founder from 0patch, in an article last week.
However, it should be noted that the vulnerability can only be exploited to accomplish elevation of privilege under specific circumstances, i.e. when the System Protection feature is enabled on C: Drive and at least one administrator account. local is configured on the computer.
Neither Windows servers nor systems running Windows 11 are affected by the vulnerability, but the following versions of Windows 10 are affected:
- Windows 10 v21H1 (32 and 64 bit) updated with November 2021 updates
- Windows 10 v20H2 (32 and 64 bit) updated with November 2021 updates
- Windows 10 v2004 (32 and 64 bit) updated with November 2021 updates
- Windows 10 v1909 (32 and 64 bit) updated with November 2021 updates
- Windows 10 v1903 (32 and 64 bit) updated with November 2021 updates
- Windows 10 v1809 (32 and 64 bit) updated with May 2021 updates

CVE-2021-24084 is also the third Windows zero-day vulnerability to resurface following an incomplete patch released by Microsoft. Earlier this month, 0patch provided unofficial fixes for a local elevation of privilege vulnerability (CVE-2021-34484) in the Windows User Profile Service that allows attackers to gain SYSTEM privileges.
Then last week, Naceri disclosed details of another zero-day flaw in Microsoft Windows Installer service (CVE-2021-41379) that could be bypassed to gain elevated privileges on devices running the latest versions of Windows, including Windows 10, Windows 11 and Windows Server 2022.

Comments are closed.